Understanding the Critical Role of a VPN in Modern Digital Life
In an era where digital vulnerabilities are growing, protecting your private data has never been more essential. A VPN encrypts your digital communications, ensuring that malicious actors, internet service providers, and third parties cannot track your online behavior. Whether you’re accessing public Wi-Fi at a hotel or managing sensitive documents, a VPN acts as an protective layer against security leaks.
Many users overlook the dangers of open connections, leaving vulnerable their credit card numbers, account details, and communication logs. By redirecting your connection through remote servers, a 快连 hides your online identity and physical whereabouts, making it extremely difficult for tracking agencies to identify you.
Selecting the Ideal VPN for Your System: A Comprehensive Comparison
Picking the right VPN service depends on your unique requirements and platform. For Windows users, look for easy navigation, high-speed connections, and advanced security. Apple loyalists should prioritize flawless operation with iCloud services, while tech-savvy users may favor configurable options.
Android and iOS users must select VPNs with compact software that reduce battery drain and data consumption. Universal access is key if you often alternate between computers, pads, and phones. Always confirm that your VPN accommodates up-to-date technologies like OpenVPN for best results.
Step-by-Step Guide to Installing a VPN on Windows
To begin, navigate to the service’s homepage using a secure browser. Locate the download section and choose the Microsoft-suited release. After acquiring the file, run the setup file and obey the step-by-step instructions.
As you install, adjust options like launch on boot and protocol selection. Activate the kill switch feature to block data leaks if the VPN drops. Lastly, sign in with your credentials and link to a node of your choice.
Optimizing VPN Usage on Apple’s Operating System
MacOS offers built-in compatibility for VPNs, but third-party apps often offer superior capabilities. Once you’ve installed, move the VPN application to your program directory. Start the app and key in your subscription details to initiate the service.
Adjust preferences such as security levels and server locations. Enable split tunneling to channel certain programs through the 快连手机版 while permitting others to use your regular connection. For extra security, integrate your VPN with security suites to stop ransomware and fraudulent links.
Securing Linux Systems with a VPN
Tech enthusiasts often favor VPNs that support command-line interfaces. Start with, updating your software repository to confirm access to the latest VPN software. Use shell prompts to deploy the VPN application, abiding by manuals provided by your vendor.
Set up network settings to simplify VPN connections during boot-up. Experienced individuals can integrate firewall rules to block non-VPN traffic. Regularly audit reports to spot anomalies and patch your VPN software to resolve security gaps.
Protecting Mobile Devices with VPNs on Google’s OS and iOS
Mobile devices are prime targets for security incidents due to their always-online nature. Get your VPN app from the official marketplace to steer clear of malicious software. Launch the app, sign in, and choose a server nearby for faster speeds.
Activate features like ad-blocking to boost your browsing experience. Adjust the VPN to auto-connect when accessing open hotspots. For iPhone owners, enable continuous protection in device settings to sustain privacy even if the app shuts down.
Advanced VPN Features to Enhance Your Privacy
Modern VPNs offer cutting-edge options that exceed simple security. A network blocker halts all internet traffic if the VPN disconnects, avoiding data exposure. Server chaining directs your connection through multiple servers, hiding your digital trail more effectively.
Threat detection systems remove malicious banners and prevent dangerous websites. Traffic division lets you decide which apps use check here the VPN, prioritizing speed and protection. For teams, fixed locations and user management facilitate protected teamwork.
Addressing Common Myths About VPNs
Despite their widespread use, many users misunderstand how VPNs work. A common myth is that VPNs completely anonymize your digital behavior. While they conceal your location, browser fingerprints can still reveal your persona. Moreover, few VPNs practice privacy-first principles, so examining your provider’s policies is essential.
A second fallacy is that VPNs dramatically reduce internet speeds. While encryption adds overhead, high-quality providers lessen this impact with efficient infrastructure. Lastly, unpaid tools often compromise protection by sharing user data or showing intrusive ads.
Future-Proofing Your Online Presence with a VPN
As technology evolves, staying protected requires preventive actions. Emerging trends like next-gen processing could challenge current protection methods, making it vital to opt for VPNs committed to upgrading their infrastructure. Integrating a VPN with extra safeguards like secure storage and multi-step verification builds a comprehensive security strategy.
Authorities worldwide are tightening digital rights regulations, and a VPN ensures you adhere with these standards. Whether you’re accessing media, engaging in eSports, or conducting business, a VPN is an indispensable tool for operating the online realm confidently.
 Scott Baio Then & Now!
Scott Baio Then & Now! Katie Holmes Then & Now!
Katie Holmes Then & Now!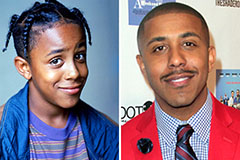 Marques Houston Then & Now!
Marques Houston Then & Now! Nancy Kerrigan Then & Now!
Nancy Kerrigan Then & Now! Dawn Wells Then & Now!
Dawn Wells Then & Now!